Thick Client Application VAPT
Talk to us now!
Thick client applications are the applications that run directly on a user's device, like desktop software. Thick client penetration testing is an assessment process aimed at evaluating the security of a desktop application by identifying vulnerabilities, testing authentication mechanisms, assessing data encryption, addressing security misconfigurations, and examining network communication to ensure the robustness and integrity of thick client software.
There are multiple benefits of getting VAPT done for your thick client application. Some of the most important are listed below.

Early Identifying of vulnerabilities allows organizations to identify and address security threats before they escalate into significant breaches.

It safeguards user data from potential breaches and unauthorized access.

It ensures adherence to data protection regulations and industry standards.

Identifying & fixing vulnerabilities improves the security posture of a thick client application.

By identifying and fixing vulnerabilities, it maintains a positive brand image and user trust.

Ensures users that their sensitive information is secure, enhancing user confidence and loyalty.
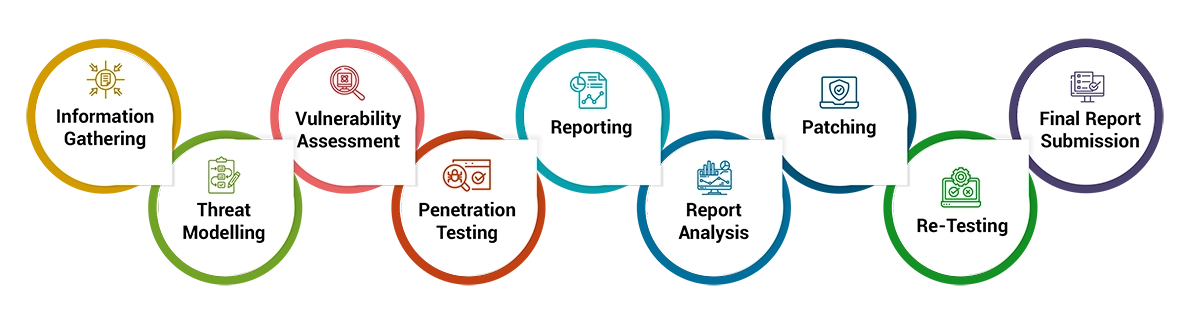
Understand the thick client application testing scope, functionalities, architecture and procure the necessary data like test login credentials, etc.
Identify potential attack vectors and scenarios specific to the thick client application.
Employ automated scanning tools and manual analysis techniques to identify vulnerabilities in the thick client application.
Simulate real-world attacks attempting to exploit vulnerabilities to understand their impacts and potential risks.
Provide a detailed report outlining identified vulnerabilities, their impacts along with the necessary remediation steps to be taken.
Development teams to address vulnerabilities based on the provided recommendations to improve the thick client application security posture.
Conduct a VAPT re-evaluation to ensure that vulnerabilities have been effectively addressed.
Deliver a final comprehensive report detailing the assessment findings & actions taken.





Contact us for more details. We are happy to help you in all cloud support related questions.